Click to learn more about author Samuel Bocetta.
For as long as there have been computer networks, there has been an ongoing arms race between those striving to keep them private and secure, and those who seek to exploit their weaknesses and use, steal, or leverage their contents for fun or profit. This Spy vs. Spy battle has formed the heart and soul of all cybersecurity.
When malicious cyberattacks on high-level targets succeed – like the December 2013 hack of major discount retailer Target, which resulted in the theft of credit and debit card information from more than 40 million customers – the financial losses and reputational damage can be grievous, but never yet have people been physically harmed or put at life-threatening risk.
Enter Triton

That, we are sad to say, has changed with the appearance of Triton, a particularly vicious form of malware that targets the Safety Implemented Systems of industrial equipment at places like oil, gas, water treatment, and chemical facilities, or even at nuclear power plants.
Normally, the Safety Implemented Systems at such facilities are meant to regulate the flow and processing of potentially hazardous industrial material. Through things like automated logic controllers, automatically administered diagnostic checks, and redundancy management systems, they aim to create cybernetic feedback loops that prevent or contain potential industrial disasters like oil spills, gas leaks, and nuclear meltdowns.
This makes them a particularly glorious demonstration of the power of the Industrial Internet of Things (IIoT), as they automate industrial safety systems and make them less prone to malfunction due to human error.
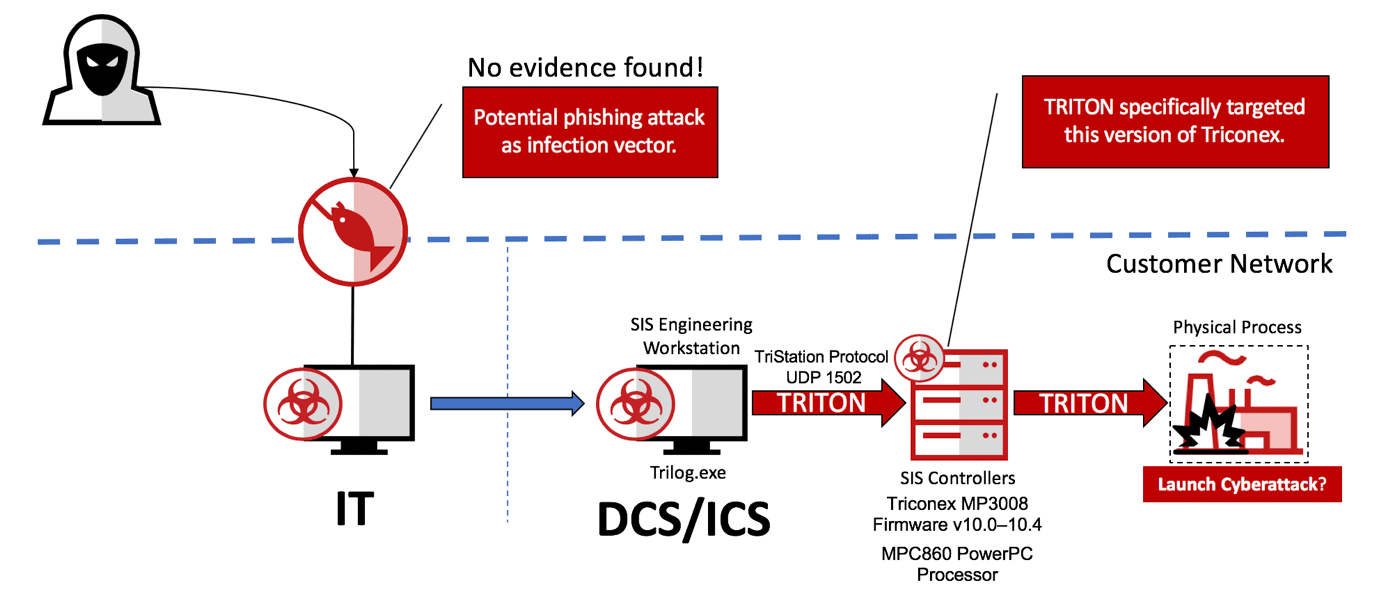
As Triton shows, however, this advantage is a double-edged sword. By connecting industrial equipment to computer networks – even ones to which access is in theory highly restricted – we risk putting that equipment under the control of malicious actors who can then cause previously undreamt-of amounts of damage.
Even worse, life and limb could be put at risk via something as simple as a network intrusion created by a simple social engineering ploy. All it takes is a single moment of inattention on the part of an employee of the facility and the hacker is in.
How Triton Reared Its Ugly Head
In the summer of 2017, Aramco, Saudi Arabia’s national oil company and the largest in the world, experienced a series of equipment malfunctions of mysterious origin. The company then called on Mandiant Consulting Services, a branch of the cybersecurity firm FireEye, to help determine the source of the problem.
According to FireEye’s report, published in December of 2017, an unknown attacker or attackers used Triton to target the Schneider Electric Triconex safety controller, a device that Aramco used to monitor, control, and secure its oil valves and turbines, and to shut them down if any significant risk of failure was detected.
Fortunately, the hackers made a few errors that made it possible to detect them and remove the threat they posed before they could significantly compromise Aramco’s systems. Had they not been stopped, the attackers could have released deadly hydrogen sulfide gas or manipulated Aramco’s Safety Implemented Systems to cause explosions or oil fires, potentially leading to great loss of life.
Further Research Into Triton
Naturally, this close call spawned great interest among hackers and cybersecurity professionals in Triton and its capabilities. In this spirit, Andrea Carcano, Marina Krotofil, and Younes Dragoni conducted some important research in 2018 on just what Triton can do and how to guard against it.
In a white paper that they published to explain their findings, they detailed the results of a simulated Triton attack that they set up in a controlled hacking lab specifically dedicated to the purpose. After obtaining the hacking tools necessary to carry out the Triton attack, the three were able to buy the components necessary to build their own Triconex controller.
They reverse engineered the TriStation suite of software that the Triconex controller uses to communicate with the different kinds of industrial equipment hooked up to an IIoT network at a typical industrial facility. From this analysis, they were able to learn how Triton compromises the TriStation software that the Triconex controller uses and were able to launch their own attack against the controller, demonstrating that an attacker could acquire control over it with Triton.
Those interested in the details of their hack, which they also presented at the 2018 Black Hat conference for hackers and cybersecurity professionals, would do well to read their white paper.
Fighting Back
Carcano, Krotofil, and Dragoni’s research led them to create two useful tools for defending against Triton attacks. The first is called the TriStation Protocol Plug-in for Wireshark. Using a data packet analysis tool called Wireshark, security engineers can examine communications between industrial devices, highlight those that look suspicious, and be alerted to the presence of a Triton attack.
The second, called the Triconex Honeypot Tool, is meant to simulate a Safety Implemented System, trick hacking tools into detecting it, and alert system administrators that there are hackers who are attempting to gather information about their systems.
There is one other important implication of Carcano, Krotofil, and Dragoni’s research: Though it is thought that some state party carried out the attack on Aramco — sources differ on whether Iran or Russia might be the culprit — the great resources that states can marshall are ultimately not necessary to carry out Triton attacks but can be done rather cheaply.
This, of course, only increases the danger that such attacks pose and makes adequate security against them all the more indispensable.
What Can Be Done?
With the very real danger to life and limb posed by Triton malware and how unquestionably vulnerable the entire Industrial Internet of Things is to it, what’s a system administrator to do? How can we guard against this threat? Here are a few general tips:
Follow good network security practices.
Use a VPN and hide your network IP address. Don’t leave it written anywhere, especially not on any company documents, as persistent hackers may even go through your trash during reconnaissance. Have strong passwords and restrict network access accordingly. For more information, Privacy Canada provides educational and technical information on installing VPNs, hiding your IP address, and implementing other online security best practices.
Be on guard against social engineering.
The term “social engineering” refers to what might be called the human element of hacking. Since modern anti-malware systems in most major computer networks are quite advanced, when hackers break in, they tend to do so by skillfully manipulating some human being into divulging a password, IP address, or some other crucial bit of information. Thanks to the fuzzy and unpredictable nature of human psychology, it can be difficult to protect your organization against social engineering attacks. Nevertheless, there are some things that you can teach your staff to keep you protected.
Use anti-Triton security tools.
Anti-Triton security tools do exist, specifically in the mentioned tools, which can be easily installed onto your network.
The Bottom Line
There’s no denying that Triton is a bad hombre that has the potential to cause chaos and destruction. The good news is that there are teams of white hat developers working to block hackers at every turn. Help is already here in the form of Artificial Intelligence and Machine Learning, including algorithms that have been deployed to help protect the American utility infrastructure. We should expect even more sophisticated strategies from this quarter in the near future.
And the deadly game continues.


