Click to learn more about author Samuel Bocetta.
For companies of all sizes, digital data is often one of their most critical assets.
As a result, information security needs to be a priority throughout the organization and not just within the IT team. Data breaches and cyberattacks can quickly infiltrate a network and cause significant damage to a company’s data, reputation, and profits.
Over much of the last decade, a leading threat within the cybersecurity industry has been ransomware attacks. During such an incident, a hacker gains access to internal systems or hardware and then locks all employees out of their data. This will usually be accompanied by a message on screen from the attacker demanding a ransom payment in order to restore full functionality.
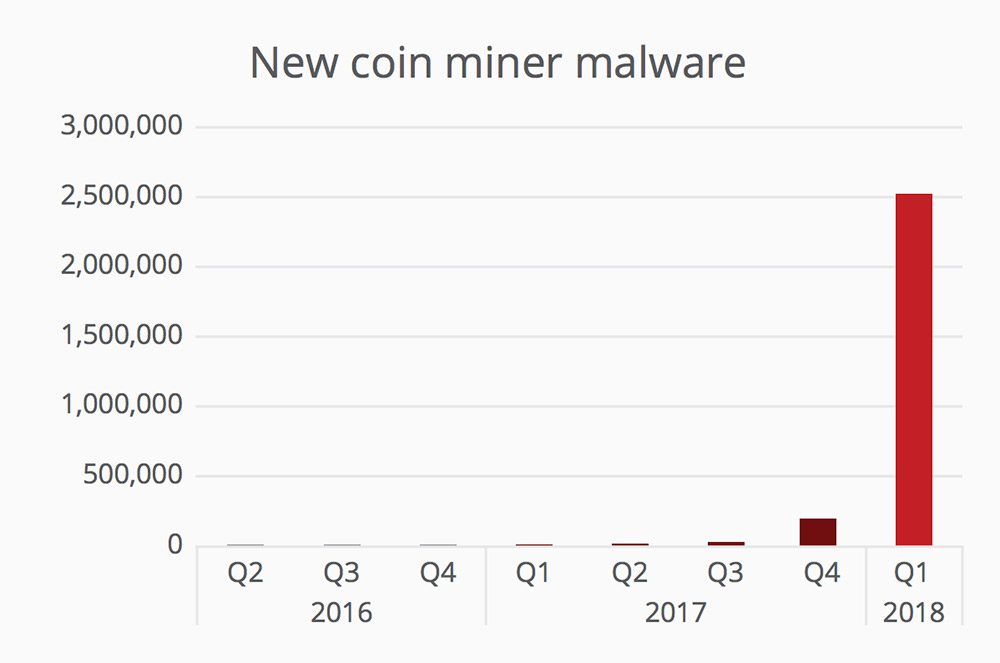
As organizations have found better ways to combat and prevent ransomware attacks, hackers have started looking towards other avenues for illicit revenue. The latest emerging threat is called cryptojacking, and this type of attack is often harder to detect than ransomware but with just as much risk for disaster.
Basics of Cryptocurrency Mining

Cryptojacking attacks revolve around the system used to create and track digital currencies like Bitcoin or Ether. These cryptocurrencies use a technology known as blockchain to allow for financial transactions to occur online without involving a central institution or bank.
As part of the blockchain network, individual users can set up hardware for mining purposes. A mining server runs a series of complex algorithms to verify different values that have entered the blockchain system. As a reward, miners receive a small amount of currency in exchange for completing the task.
Although mining for cryptocurrency can be a profitable endeavor, the amount of hardware and electricity required to run such an operation is expensive. As a result, many cybercriminals have looked for alternative solutions.
That is how the cryptojacking trend emerged on the scene.
How Cryptojacking is Executed

The majority of cryptojacking attacks begin with a traditional phishing attempt, often through email. You may receive a message from a sender that looks to be related to a legitimate company or bank account, but when you read through the content some of it will look suspicious.
The phishing message contains one or more hyperlinks within the text, normally disguised to look like they are pointing to a useful website. After clicking on one of these links, your web browser will be directed to a rogue page that may initiate a background download of malicious software.
Some cryptojacking viruses are spread directly over an infiltrated network. This is especially common among users who access the internet from public wi-fi hotspots. To protect against that, organizations should enforce that employees must use a virtual private network (VPN) client on any company-owned hardware.
Once the cryptojacking virus has been downloaded to your local hard drive, it runs in the background of your other CPU processes. The malware is designed to compute algorithms for a specific form of cryptocurrency and can typically hog more than 90 percent of your computer’s processing and memory resources.
At periodic times, the cryptojacking virus will redirect all earned blockchain funds into an anonymous digital wallet owned by the hacker.
Detecting a Cryptojacking Attack
With a ransomware attack, the hacker wants you to become aware of the exploit right away in order to extort a payment from you. Cryptojacking operates in the exact opposite fashion. Cryptojackers want to run their scheme for as long as possible without the organization noticing, because that will allow them to mine more digital currency while using someone else’s hardware and electricity.
From an organizational point of view, the best thing to do regarding cryptojacking is to educate your userbase and employees. Cryptojacking viruses may not be visible on screen, but there are several checks that can be done if you are concerned that your company’s hardware has been infected.
An organization can use operating system monitoring tools to check the current levels of CPU and memory usage on their network of PCs and servers. Cryptojacking viruses will hog high percentages of both metrics for an extended period of time, so if you see certain devices exhibiting those symptoms, there is a good chance they could be infected.
Computers affected by a cryptojacking attack typically suffer poor performance and may run at a hotter temperature while internal fans attempt to keep up with the CPU usage. Organizations need to pay attention to any user reports of a system running unusually slow or being hot to the touch. The aptly named “Core Temp” is a simple, free piece of software that tells you if and when your CPU overheats. Just beware: some purported CPU temp checking applications themselves have malware, which ironically can expose you to a cryptojacking attack!
Protecting Your Organization
Cryptojacking attacks can hit an organization at any time, so it’s important for security teams and leaders to remain diligent about the threat. Companies need to invest heavily in malware detection and prevention to ensure that hackers are unable to infiltrate their systems even if a user accidentally clicks a rogue link.
Many intrusion detection systems are available on the market today with functionality designed to specifically watch for viruses related to cryptojacking. These scanners function like a smart firewall that can monitor all incoming traffic from the open internet and block any requests that are automatically flagged as suspicious.
Having a reliable backup and recovery system can save an organization from much of the damage that a cryptojacking attack will cause. In a worst-case scenario, an affected piece of hardware will be unusable due to the mining operation running in the background. If this happens, wiping the internal hard drive and restoring to a saved backup is the best solution.
Final Thoughts
Above all else, make sure to emphasize the risks of cryptojacking while educating your userbase.
Employees should have a mandated security training on a regular basis, quarterly if possible, where they are taught about emerging threats like cryptojacking and methods for detecting a potential phishing attempt.


