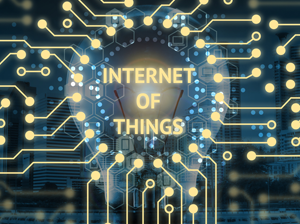
“System using multiple technologies, ranging from the Internet to wireless communication and from micro-electromechanical systems (MEMS) to embedded systems. The traditional fields of automation (including the automation of buildings and homes), wireless sensor networks, GPS, control systems, and others.”
Other Definitions of IOT include:
- “A more comprehensive view of operations via new data points, in previously uncharted territories,” in a data context. (Shawn Ryan)
- “Any device with an on/off switch connected to the Internet. This includes almost anything you can think of, ranging from cellphones to building maintenance to the jet engine of an airplane.” (Keith Foote, DATAVERSITY®)
- “Links between the physical and digital worlds.” (Munich and San Ramon, The Economist)
- “The network of physical objects that contain embedded technology to communicate and sense or interact with their internal states or the external environment.” (Gartner)
- “Exchange of data between sensors and connected devices.” (Buccola et al., MIT Sloan Management Review)
- A” network of internet-connected objects able to collect and exchange data using embedded sensors.” (Andrew Meola, Business Insider)
- Every Day “objects that can be connected to the internet and be recognized by other devices and contribute info to a database.” (Bernard Marr, Forbes)
Businesses Use the Internet of Things (IoT) to:
- Grow the organization.
- Leverage new data sources.
- Develop new services.
- Track goods in a Supply Chains.
- Meet customer demands and needs.
- Price customers dynamically.
- Recommend goods to customers.
- Help with predictive maintenance.
Photo Credit: Zapp2Photo/Shutterstock.com